TIM’s Red Team Research led by Massimiliano Brolli discovered 6 new zero-day vulnerabilities in Schneider Electric StruxureWare.
Today, TIM’s Red Team Research led by Massimiliano Brolli, discovered 6 new vulnerabilities in the StruxureWare product. The flaws have been addressed by the manufacturer Schneider Electric, between April and November 2020.
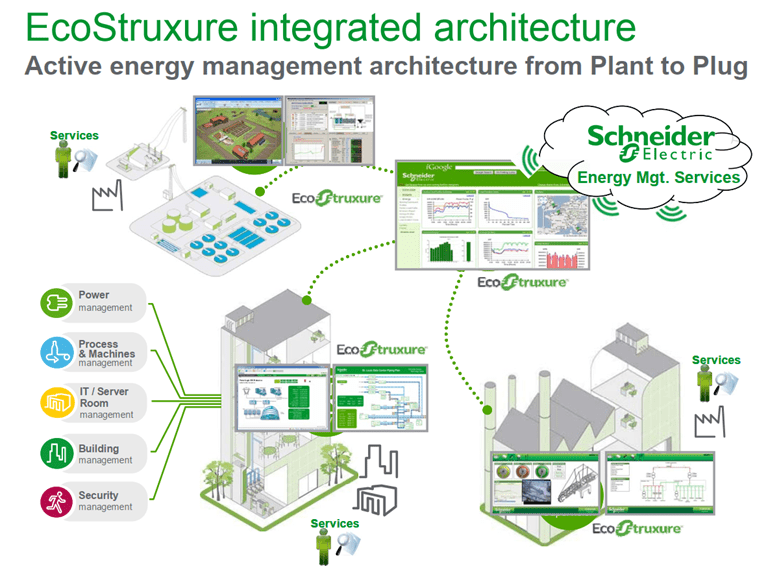
Schneider Electric is a vendor specialized in energy and automation products, like ICS, SCADA and IoT products. StruxureWare Building Operation is a software integrated with physical devices for integrated monitoring, control, and management of energy, lighting, fire safety, and HVAC.
Below the list of vulnerabilities discovered by the TIM’s Red Team Research team:
| CVE | Vulnerability | Severity |
| CVE-2020-7569: | Upload of File with Dangerous Type | 8.8 |
| CVE-2020-7572 | Improper Restriction of XML External Entity Reference | 8.8 |
| CVE-2020-28209 | Windows Unquoted Search Path | 7.0 |
| CVE-2020-7570 | Cross-Site Scripting Stored | 5.4 |
| CVE-2020-7571 | Cross-Site Scripting Reflected | 5.4 |
| CVE-2020-7573 | Improper Access Control | 6.5 |
The issues were discovered during laboratory tests, promptly managed in a CVD (Coordinated Vulnerability Disclosure) process with the vendor.
The laboratory has been active for less than a year (based on the CVE recorded on the national Vulnerability Database), the experts also discovered unknown vulnerabilities in various products, including NOKIA, Wowza, Selesta, Flexera, Oracle and Siemens.
The research team has identified a total of 31 published CVEs, an average of one CVE every 11 days and this is the result of a great job that TIM is doing, especially in the Bug Hunting activities, where the Italian cybersecurity community should do much more.
The full list of CVEs discovered by the researchers is available at the TIM Corporate websites:
https://www.gruppotim.it/redteam
TIM is a leading Italian telco carrier, it is one of the few Italian industrial realities that dedicate an important effort in conducting research of undocumented vulnerabilities, for this reason, I suggest you follow them.
(SecurityAffairs – hacking, Schneider Electric)
Share On
Pierluigi Paganini
Pierluigi Paganini is member of the ENISA (European Union Agency for Network and Information Security) Threat Landscape Stakeholder Group and Cyber G7 Group, he is also a Security Evangelist, Security Analyst and Freelance Writer. Editor-in-Chief at “Cyber Defense Magazine”, Pierluigi is a cyber security expert with over 20 years experience in the field, he is Certified Ethical Hacker at EC Council in London. The passion for writing and a strong belief that security is founded on sharing and awareness led Pierluigi to find the security blog “Security Affairs” recently named a Top National Security Resource for US. Pierluigi is a member of the “The Hacker News” team and he is a writer for some major publications in the field such as Cyber War Zone, ICTTF, Infosec Island, Infosec Institute, The Hacker News Magazine and for many other Security magazines. Author of the Books “The Deep Dark Web” and “Digital Virtual Currency and Bitcoin”.
TIM’s Red Team Research led by Massimiliano Brolli discovered 6 new zero-day vulnerabilities in Schneider Electric StruxureWare.
Today, TIM’s Red Team Research led by Massimiliano Brolli, discovered 6 new vulnerabilities in the StruxureWare product. The flaws have been addressed by the manufacturer Schneider Electric, between April and November 2020.

Schneider Electric is a vendor specialized in energy and automation products, like ICS, SCADA and IoT products. StruxureWare Building Operation is a software integrated with physical devices for integrated monitoring, control, and management of energy, lighting, fire safety, and HVAC.
Below the list of vulnerabilities discovered by the TIM’s Red Team Research team:
| CVE | Vulnerability | Severity |
| CVE-2020-7569: | Upload of File with Dangerous Type | 8.8 |
| CVE-2020-7572 | Improper Restriction of XML External Entity Reference | 8.8 |
| CVE-2020-28209 | Windows Unquoted Search Path | 7.0 |
| CVE-2020-7570 | Cross-Site Scripting Stored | 5.4 |
| CVE-2020-7571 | Cross-Site Scripting Reflected | 5.4 |
| CVE-2020-7573 | Improper Access Control | 6.5 |
The issues were discovered during laboratory tests, promptly managed in a CVD (Coordinated Vulnerability Disclosure) process with the vendor.
The laboratory has been active for less than a year (based on the CVE recorded on the national Vulnerability Database), the experts also discovered unknown vulnerabilities in various products, including NOKIA, Wowza, Selesta, Flexera, Oracle and Siemens.
The research team has identified a total of 31 published CVEs, an average of one CVE every 11 days and this is the result of a great job that TIM is doing, especially in the Bug Hunting activities, where the Italian cybersecurity community should do much more.
The full list of CVEs discovered by the researchers is available at the TIM Corporate websites:
https://www.gruppotim.it/redteam
TIM is a leading Italian telco carrier, it is one of the few Italian industrial realities that dedicate an important effort in conducting research of undocumented vulnerabilities, for this reason, I suggest you follow them.
(SecurityAffairs – hacking, Schneider Electric)




